
Difference Between Next-Generation Firewalls (NGFW) Vs Traditional Firewalls
The digital world is continuously growing, and so are the dangers to your business. The protective spine of any company is its firewall, working as the major gatekeeper between your protected internal network and the chaotic external internet. For years, the traditional firewall was the standard.
But as cyberattacks have become more intelligent and more complicated, a new breed of protection has emerged: the Next-generation firewall. Understanding the difference between these two firewalls is crucial for any company, particularly those that are in search of strong firewall installation to secure their valuable assets.
Table of Contents
What is a Traditional Firewall?
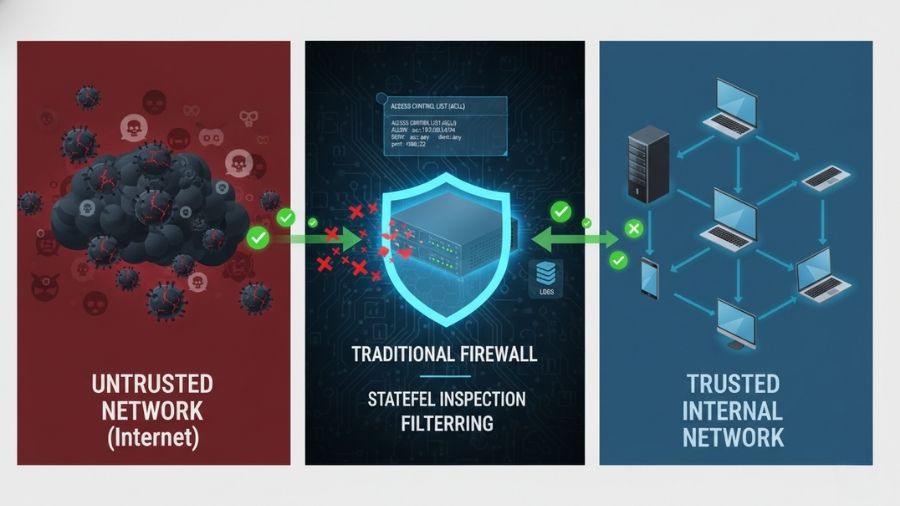
Consider a traditional firewall as a protection at the entrance of a building. Its job is easy – check the ID on every package coming in or going out. A traditional firewall runs majorly at the lower layers of the network. Its main operations are –
1. Packet Filtering – It examines the header of a data packet against a predefined collection of regulations. In case the packet matches a rule, it’s permitted; otherwise, it is banned.
2. Stateful Verification – It monitors the situation of active connections. This means it remembers legal outgoing approaches and permits the corresponding incoming replies, delivering a better level of protection than simple packet filtering.
The Limitations of Traditional Firewalls

While conventional firewalls are still crucial for common network segmentation and control, they fall short in today’s landscape because they can’t see what is inside the data packet. They are port-and protocol-centric.
1. Application-Layer Attacks – Several advanced applications utilize standard, open ports. A traditional firewall would see an application utilizing a standard port and let it through, even if it is holding negative content or being utilized for unknown objectives.
2. Advanced Malware and Zero-Day Exploits – Since they do not examine the actual content, they cannot find sophisticated malware hidden within a seemingly legal data stream.
3. Encrypted Traffic (SSL/TLS) – Most internet traffic today is encrypted. A traditional firewall can only watch the traffic that is encrypted and let it pass, which is a huge blind spot for cybercriminals hiding dangers.
What is a Next-Generation Firewall?

The next-generation firewall is the growth of the traditional firewall, designed particularly to tackle the complications of advanced cyber threats. It is not only a gatekeeper; it is a protected center with many profound verification abilities.
An NGFW merges the common operations of a traditional firewall the several modern protection features in a single, integrated platform. This change moves the firewall from being a passive access control point to an active threat prevention system.
Key features of next-generation Firewalls
NGFWs run all the way up to Layer 7, providing them a complete perspective of the network traffic. Here are the major features that established NGFWs apart –
1. Deep Packet Inspection (DPI) and Application Awareness
NGFWs employ Deep Packet Inspection (DPI) to examine the complete content, or “payload,” of the data packet, in contrast to conventional firewalls that only examine the packet header.
- What it means – An NGFW can determine the precise application sending or receiving the data, no matter the port or protocol it is utilizing.
- The Benefit – This application awareness permits a manager to make guidelines depending on applications. For instance, you can permit a corporation’s sales team to utilize a particular CRM application but block streaming video or social media to save bandwidth and control distraction, even if they all utilize the same web browser and port.
2. Integrated Intrusion Prevention System
This is one of the most crucial features. An IPS actively supervises network traffic for negative activity and renowned threat patterns.
- What it means – In case the NGFW protects an attack signature, it instantly blocks the traffic and controls the intrusion, instead of only logging it like older systems.
3. Identity and User Control
NGFW can tie protection guidelines to individual users and user groups, not only static IP addresses.
- The Benefit – If a worker is trying to access a limited network resource, the NGFW understands who they are, not only which computer they are utilizing, making protection guidelines more accurate and simpler to handle across a vibrant environment.
4. Advanced Threat Protection and Intelligence
NGFWs are developed to combat the current dangers, including modern persistent threats and zero-day attacks.
- Key Tools – They usually incorporate cloud-based threat intelligence feeds, URL filtering, and even sandboxing – a method where suspicious files are isolated and detonated in a secure virtual environment to determine in case they contain malware before they enter the major network.
5. SSL/TLS Decryption and Inspection
As previously stated, traditional firewalls have a significant blind spot when it comes to encrypted traffic. Before sending encrypted traffic to its destination, NGFWs can decrypt it, check it for hidden threats, and then re-encrypt it. This is essential for identifying malware that is concealed on secure websites.
NGFW Vs. Traditional Firewall – A Simple Comparison
| Feature | Traditional Firewall | Next-Generation Firewall (NGFW) |
| Inspection Depth | Looks at Packet Headers (IP/Port/Protocol). | Uses Deep Packet Inspection (DPI) to look at the Content/Payload. |
| Network Layers | Operate at Layers 3 and 4 (Network & Transport). | Operates up to Layer 7 (Application Layer). |
| Application Control | No. Filters traffic only based on ports. | Yes. Can identify, monitor, and block specific applications. |
| Threat Prevention | Basic packet filtering and stateful inspection. | Advanced. Includes Integrated IPS, Anti-Malware, and Sandboxing. |
| User Awareness | No. Policies are based only on IP addresses. | Yes. Policies are based on User Identity and Group. |
| Modern Threat Defense | Poor. Vulnerable to application-layer attacks and malware in encrypted traffic. | Excellent. Designed to detect sophisticated threats, including zero-day and malware in SSL traffic. |
Secure Your Digital Future with a Web Application Firewall Solution Dubai

Staying ahead of cyber threats is a must for UAE businesses. Even though the NGFW offers complete network security, contemporary cloud apps and web services need an additional line of protection. A web application firewall solution in Dubai becomes crucial in this situation.
The purpose of a Web Application Firewall (WAF) is to defend web applications (such as your website, e-commerce platform, or customer portals) against common application layer attacks like SQL injection and Cross-Site Scripting (XSS). The network is protected by an NGFW, but the applications that use the network are protected by a WAF.
A crucial investment is selecting the appropriate security architecture, ranging from the fundamental NGFW to specialized WAF protection. In order to ensure that your network is safeguarded by the newest, most efficient technologies catered to your company’s requirements, companies such as Bluechip Computer Systems offer professional consulting and implementation services for advanced firewall installation in Dubai.
Ultimately, the reality of today’s threat landscape necessitates the comprehensive, integrated security offered by a Next-Generation Firewall, even though a Traditional Firewall may provide a basic defense.
Don’t accept security from the past; instead, invest in intelligent, multi-layered security to secure your company for the future.
Also Read: Structured Cabling In Dubai: Why Your New Office Network Is Only As Good As Its Wiring









